Management Approach
Cybersecurity
Integrated Cybersecurity Management Framework
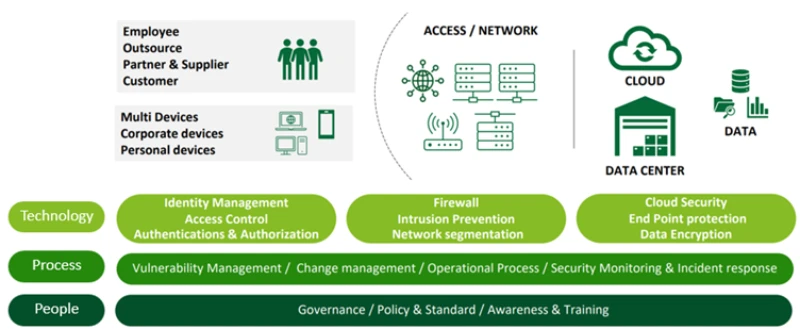
Technology
AIS deploys comprehensive cybersecurity technologies across devices, networks, systems, and data environments. These include intrusion detection and prevention systems, data encryption, and advanced cloud security solutions designed to enhance the Company’s ability to prevent, detect, and respond to cyber threats effectively and in a timely manner.
Process
The Company establishes structured security standards and control processes covering access management, vulnerability assessment and mitigation, and incident response. These processes are aligned with applicable laws and internationally recognized standards to ensure consistent, robust, and effective risk management.
People
Clear roles and responsibilities for cybersecurity are defined across the organization to ensure accountability and effective oversight. AIS continuously invests in capability development and fosters a strong security culture among employees and business partners, promoting the responsible and secure use of systems and data across its value chain.
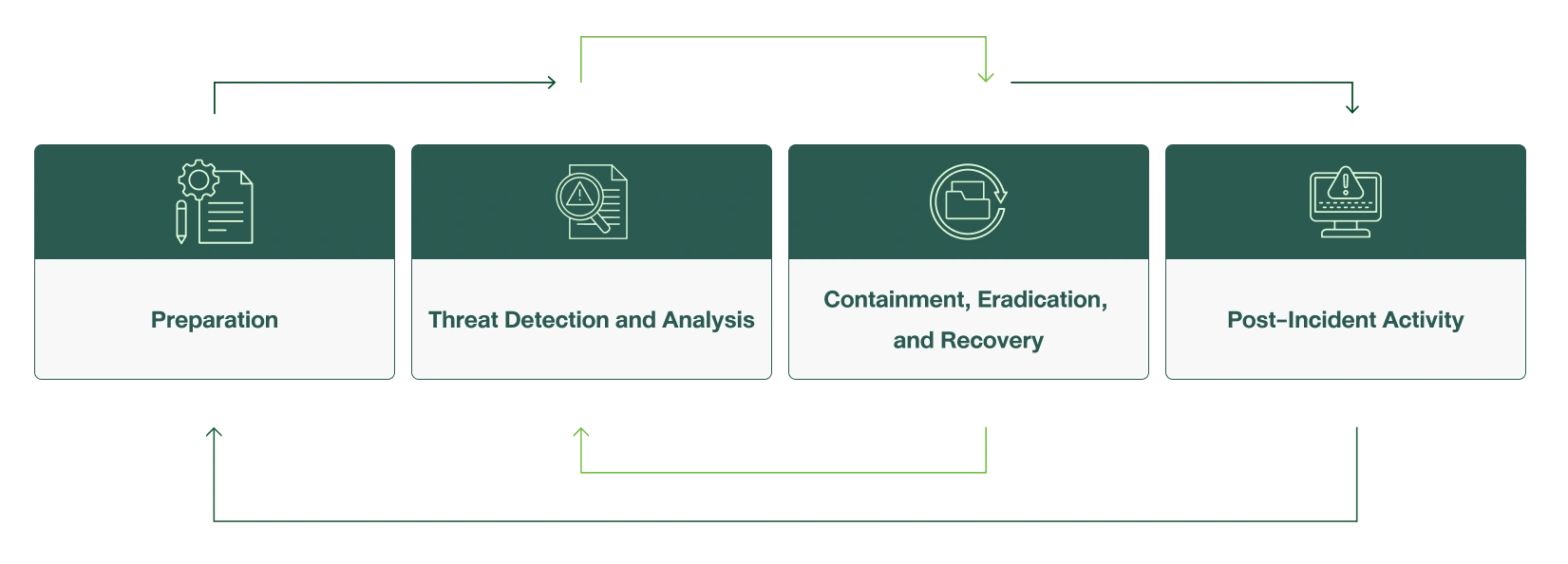
Cybersecurity framework and process
Cyber Threat Management and Response Framework

Customer Privacy Protection
Personal data protection framework and process
Managing data governance
- Establish personal data protection policies for AIS Group
- Develop and publish the AIS Group Privacy Notice
- Review and/or update policies, standards, and guidelines at least once a year.
- Determine confidentiality classification, including access to sensitive information and utilizes various data protection tools and techniques to safeguard information.
- Formulate data flow specification in a system manner
- Establish customer data protection standards through a structured Data Life Cycle Management process, covering how employees and relevant third parties handle customer data throughout its lifecycle.
Awareness raising and training
- Promote awareness of personal data protection in term of data life cycle management
- Promote the principles of “Privacy by design” and “Privacy by default” for responsible product and service design
Risk follow-up and assessment
- Conduct a Data Protection Impact Assessment (DPIA) in accordance with internationally recognized standards
- Assess risk from daily operations
- Define standard contractual clauses (SCCs) with related units
- Prepare records of personal data processing
- Establish an internal audit team to construct an annual audit plan
Personal data breach prevention and response
- Establish protocol for disciplinary action in the occurrence of a personal data breach
- Establish the Incident Center to be responsible for responding to personal data breaches and cyberattacks
Data Breach Response Procedure
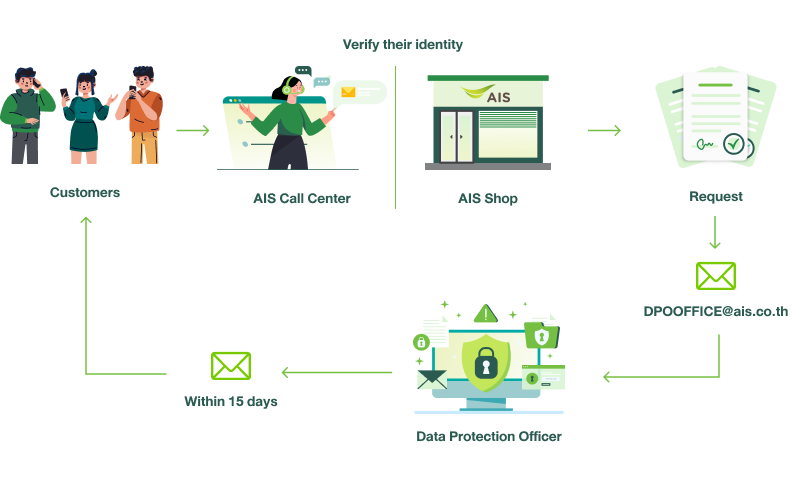
Procedure for Processing Customer Request
Certifications and Accreditations in Cybersecurity and Data Protection
















International Standards Certification for Cybersecurity and Customer Data Protection




Performance Table
| Topic | Units | 2022 | 2023 | 2024 | 2025 |
|---|---|---|---|---|---|
| Personal data protection | |||||
| Number of personal data breach and data loss complaints | |||||
|
Complaints from general persons or agencies
|
Number of cases | 7 | 4 | 3 | 2 |
|
Complaints from regulatory agencies
|
Number of cases | 11 | 4 | 7 | 3 |
| Data leakage, theft, or loss | Number of cases | 2 | 1 | 0 | 0 |
| Requests for customers’ personal data from public agencies with the power and duty 1 | Number of cases | 19,454 | 19,255 | 19,854 | 24,653 |
|
% of the total number of requests
|
% | 92 | 92 | 93 | 96 |
| Network | |||||
|
Average frequency of network failure
|
Units | 0.07 | 0.09 | 0.07 | 0.15 |
|
Average length of network failure 2
|
Minutes | 38 | 37 | 72 | 223 |
1 The Company discloses customers’ service usage information to government authorities in accordance with their legal mandates, including the Courts of Justice, the Royal Thai Police, and the Anti-Money Laundering Office, among others.
2 In 2025, the average network downtime increased due to prolonged flooding and widespread inundation across multiple areas. These events led to extended power outages, resulting in disruptions to the telecommunications network’s power supply and longer-than-usual system recovery times.